Cyberattacks are becoming more sophisticated, particularly as enterprises migrate to the cloud. Attackers leverage automation and AI to exploit vulnerabilities in mobile devices, which serve as primary access points to valuable cloud-stored data.
This means the shift to cloud computing has widened the attack surface, increasing risks from misconfigurations and identity abuse, particularly in mobile and remote work environments. In addition, generative AI has further enhanced social engineering and ransomware attacks, enabling threat actors to create very convincing phishing messages and adapt tactics quickly once they gain access.
As organizations face these high-stakes threats, protecting enterprise devices is crucial to prevent financial, legal, and reputational damage, while also ensuring compliance with data regulations. Read on to learn about the top five challenges enterprises will face in 2026!
Table of contents:
- The top 5 mobile device security threats enterprises will face this year
- How to safeguard enterprise devices
- Keep your enterprise safe with Samsung Knox
The top 5 mobile device security threats enterprises will face this year
1. Ransomware via mobile entry points
Ransomware now causes over 40% of reported breaches as mobile devices are deeply embedded in cloud access, identity workflows, and day-to-day business operations. Once a mobile device is compromised through phishing, smishing, malicious apps, or stolen credentials, it can provide attackers with a direct pathway into corporate cloud environments (read that again if you need to).
Modern ransomware campaigns no longer rely solely on encrypting endpoints; they exploit mobile access to move laterally, harvest identities, and trigger attacks across connected systems. With generative AI enabling faster reconnaissance, more convincing social engineering, and adaptive attack techniques, ransomware can spread more quickly through mobile-connected environments, amplifying its financial, operational, and reputational impact on enterprises.
2. AI-driven social engineering
Generative AI has dramatically improved the quality, speed, and scale of mobile-focused social engineering. Highly convincing text messages, messaging app impersonations, voice deepfakes, and QR-based phishing attacks are harder for users to detect and easier for attackers to automate, making mobile users a prime target!
3. Unmanaged and BYOD devices accessing enterprise data
As hybrid and remote work continues, more employees access corporate systems from personal or unmanaged devices. As you’d expect, without proper controls, visibility, and enforcement, these devices increase the risk of data leakage, credential compromise, and policy violations, especially when accessing cloud apps and SaaS platforms.
Many of these devices lack basic security measures such as OS updates, device encryption, or endpoint protection, creating blind spots for IT teams. As a result, organizations often have limited ability to detect threats, enforce security policies, or respond quickly when a mobile device is compromised.
4. MFA fatigue and password spray attacks
As organizations strengthen identity controls, attackers have shifted their focus to the identity systems themselves. Usernames, passwords, and authentication processes are now prime targets, especially as mobile devices are central to accessing cloud apps, email, and Software-as-a-Service (SaaS) platforms.
Two techniques are particularly common—password spraying and multi-factor authentication (MFA) fatigue attacks:
- In a password spraying attack, attackers attempt to use a single, commonly used password across multiple accounts, rather than repeatedly targeting a single user. This approach helps them avoid account lockouts and detection and is especially effective against legacy authentication methods that don’t support MFA. If older login protocols are still enabled, they can provide attackers with an easy entry point.
- MFA fatigue attacks target users through their mobile devices. After obtaining a password, attackers repeatedly trigger MFA requests, flooding a user’s phone with push notifications. Over time, users may approve a request out of habit or frustration, unintentionally granting access.
5. Software supply chain and SaaS attacks
As enterprises rely more heavily on third-party software, cloud services, and SaaS platforms, attackers are increasingly targeting the software supply chain instead of individual users. By compromising a trusted vendor or third-party integration, attackers can gain indirect access to multiple organizations simultaneously without triggering traditional security alerts.
Mobile environments are especially exposed. Compromised SDKs, malicious app updates, and vulnerable mobile integrations can introduce threats directly onto employee devices, where they inherit trusted permissions and access to corporate data. Similarly, SaaS platforms accessed primarily through mobile apps can become attack vectors when APIs, OAuth permissions, or integrations are abused.
In 2026, software supply chain and SaaS attacks are particularly dangerous because they blur the line between trusted and untrusted software. A single compromised update or integration can spread rapidly across mobile and cloud environments, making continuous monitoring essential for enterprise mobile security.
How to safeguard enterprise devices
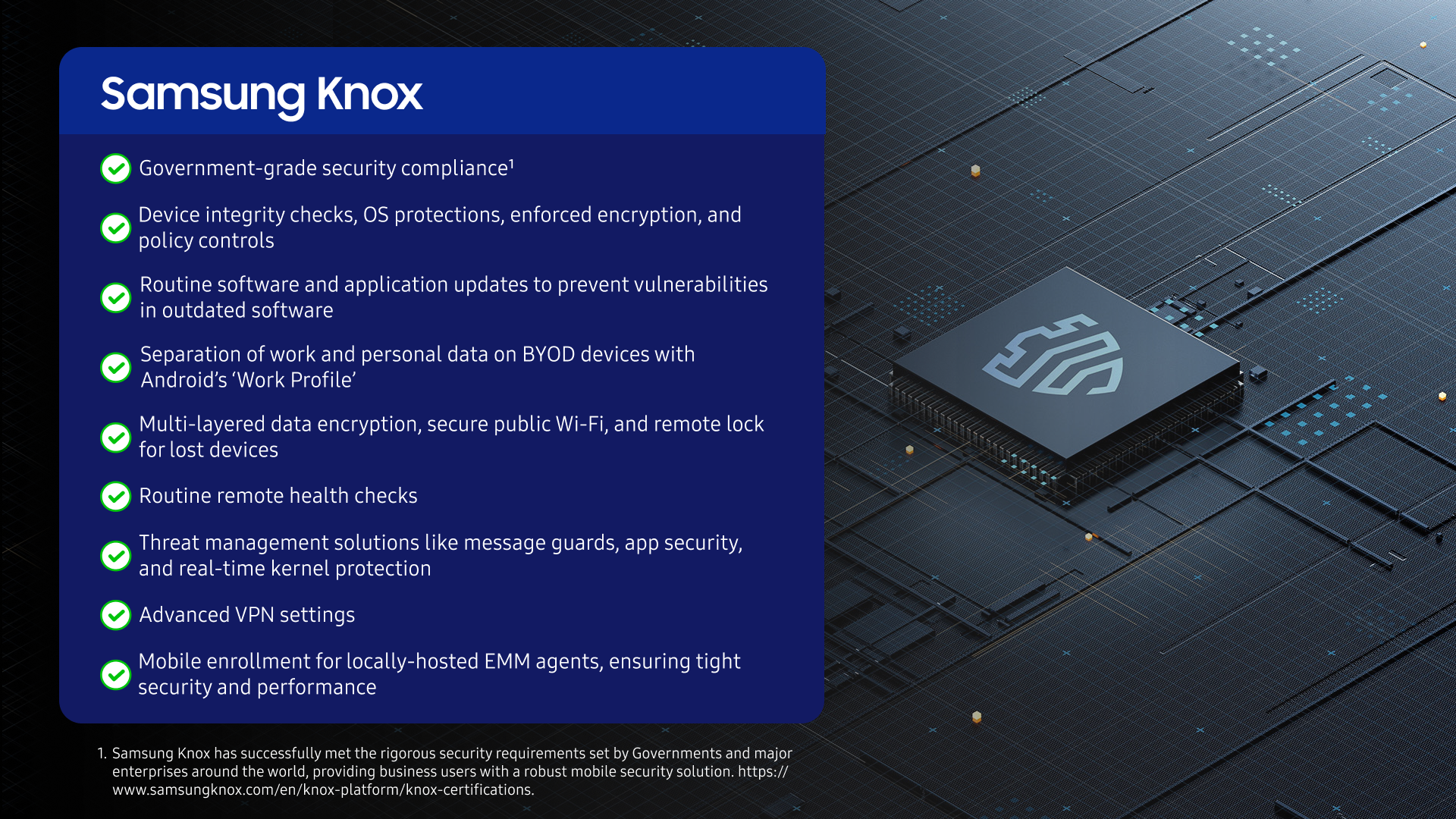
With these looming threats associated with mobile device security, protection against the big five is crucial. Security solutions, such as Samsung Knox Suite, introduce robust services to safeguard work devices and data.
Compatible with Samsung Galaxy devices, Samsung Knox Suite plans provide organizations with:
Keep your enterprise safe with Samsung Knox
As enterprise mobility continues to grow, so do mobile device security threats and vulnerabilities. Attackers are increasingly using automation and AI to scale attacks, adapt tactics, and exploit mobile access points more quickly.
To keep pace, enterprises must remain vigilant and implement robust, consistent mobile security controls. Knox Platform for Enterprise helps safeguard devices and data, ensuring compliance and reducing risk amid the rising complexity of cyberattacks in 2026.
Try Knox Suite for free for 90 days!
